Lots of of Ethereum wallets that had sat untouched for years have been drained into the identical tagged handle, turning outdated key publicity into this week’s sharpest crypto safety warning.
On Apr. 30, WazzCrypto flagged the incident affecting mainnet wallets on X, and their warning unfold rapidly as a result of the affected accounts didn’t look like freshly baited scorching wallets. They have been outdated wallets with quiet histories, some tied to belongings and tooling from an earlier Ethereum period.
Over 260 ETH, roughly $600,000, was drained from lots of of dormant wallets. Greater than 500 wallets look like affected, with losses totaling roughly $800,000, and plenty of wallets have been idle for 4 to eight years. The associated Etherscan handle is labeledFake_Phishing2831105, and exhibits 596 transactions, and data a 324.741 ETH motion to THORChain Router v4.1.1 across the Apr. 30 window.
The fixed throughout them is extra vital for now: long-idle wallets have been moved to a typical vacation spot, whereas the compromise path stays unresolved.
That unresolved vector makes the drain the strongest warning this week, following a surge in DeFi hacks. Protocol exploits often give investigators a contract, a operate name, or a privileged transaction to examine.
Right here, the central query sits on the pockets layer. Did somebody get hold of outdated seed phrases, crack weakly generated keys, use leaked private-key materials, abuse a software that after dealt with keys, or exploit one other path that has but to floor?
Public dialogue has produced theories together with weak entropy in legacy pockets instruments, compromised mnemonics, trading-bot key dealing with, and LastPass-era seed storage. One affected person personally raised the LastPass principle.
The sensible recommendation for customers is restricted however pressing. Idleness doesn’t mitigate private-key threat. A pockets with worth is dependent upon the complete historical past of the important thing, the seed phrase, the gadget that generated it, the software program that touched it, and each place that secret might have been saved.
For customers, the response might be to stock high-value outdated wallets, transfer funds solely after establishing recent key materials by trusted {hardware} or trendy pockets software program, and keep away from coming into outdated seeds into checkers, scripts, or unfamiliar restoration instruments. Revoking approvals helps for protocol publicity, together with Wasabi’s person warning, however a direct pockets drain factors first to key safety moderately than token approvals.
April widened the management floor
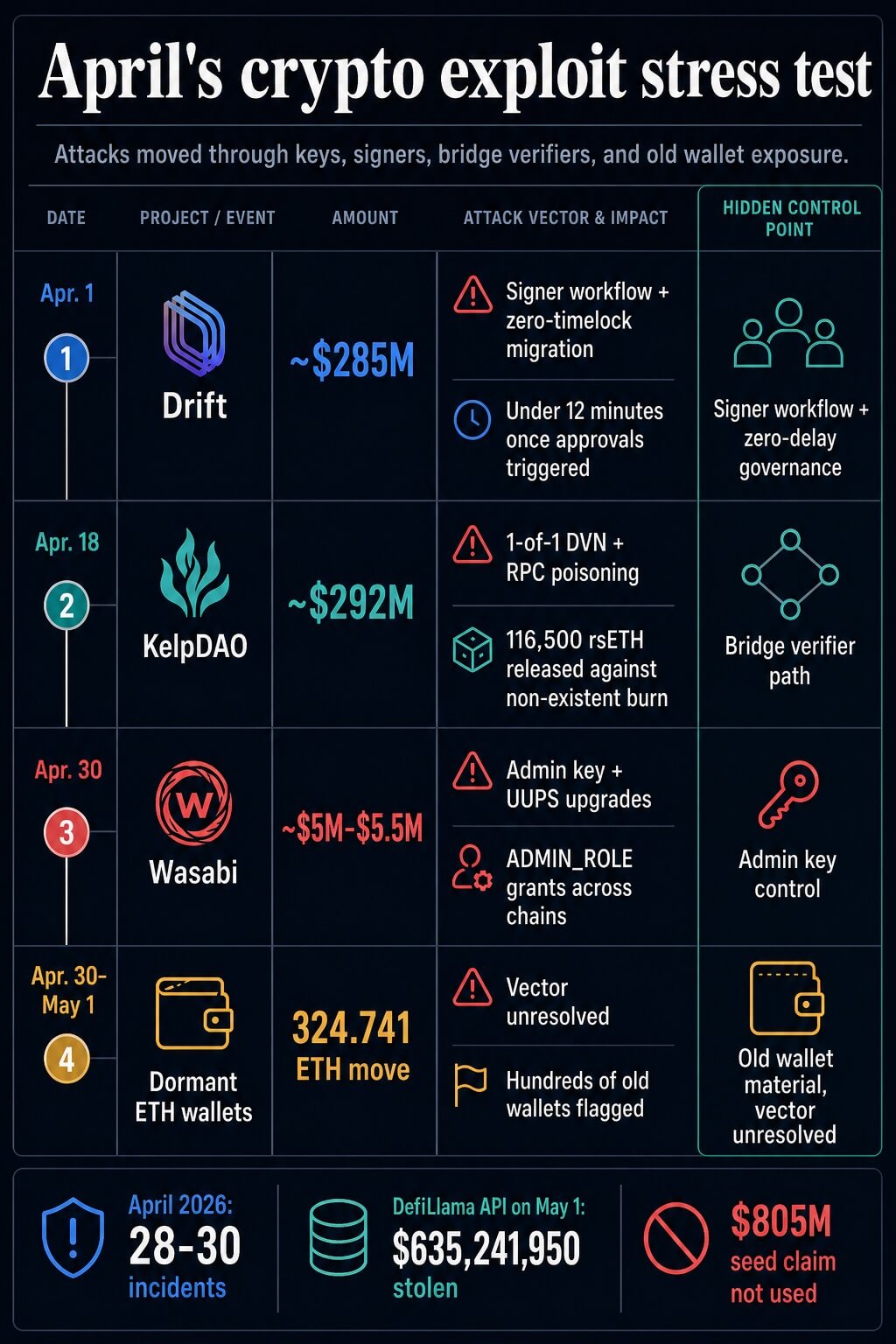
The pockets cluster landed amid April’s crypto exploit tally, which was already elevated. DefiLlama-linked reporting put April at roughly 28 to 30 incidents and greater than $625 million in stolen funds. As of Could 1, the dwell DefiLlama API confirmed 28 April incidents totaling $635,241,950.
A Could 1 market thread captured the stress level: this week’s pockets drains, Wasabi Protocol’s admin-key exploit, and April’s bigger DeFi losses all hit management surfaces that atypical customers not often examine. The hyperlink throughout the month is architectural moderately than attributional.
Admin paths grew to become assault paths
Wasabi Protocol provides the clearest current protocol instance. The Apr. 30 exploit reportedly drained roughly $4.5 million to $5.5 million after an attacker gained deployer/admin authority, granted ADMIN_ROLE to attacker-controlled contracts, and used UUPS proxy upgrades to empty vaults and swimming pools throughout Ethereum, Base, and Blast. Early security alerts flagged the admin-upgrade sample because the assault unfolded.
The reported mechanics put key administration on the heart of the incident. Upgradeability might be regular upkeep infrastructure. Concentrated improve authority turns that upkeep path right into a high-value goal. If one deployer or privileged account can change implementation logic throughout chains, the boundary round an audited contract can vanish as soon as that authority is compromised.
That’s the user-facing downside hidden inside many DeFi interfaces. A protocol can current open contracts, public entrance ends, and decentralization language whereas vital improve energy nonetheless sits in a small set of operational keys.
Signers and verifiers carried the most important losses
Drift pushed the identical management downside into signer workflow. Chainalysis described social engineering, sturdy nonce transactions, pretend collateral, oracle manipulation, and a zero-timelock 2-of-5 Safety Council migration. Blockaid put the loss round $285 million and argued that transaction simulation and stricter co-signer insurance policies might have modified the end result.
The Drift case issues right here as a result of the trail didn’t depend upon a easy public-function bug. It trusted a workflow the place legitimate signatures and quick governance equipment may very well be turned towards a hostile migration. A signer course of grew to become the management floor.
KelpDAO moved the stress take a look at into cross-chain verification. The incident assertion described a bridge configuration wherein the rsETH route used LayerZero Labs as the only real DVN verifier. Forensic critiques described compromised RPC nodes and DDoS stress feeding false knowledge to a single-point verification path.
The consequence, in keeping with Chainalysis, was 116,500 rsETH, value roughly $292 million, launched towards a non-existent burn. The token contract might stay intact whereas the bridge accepted a false premise. That’s the reason a verifier failure can change into a market-structure downside as soon as the bridged asset sits inside lending markets and liquidity swimming pools.
AI belongs within the velocity dialogue
I believe Venture Glasswing deserves a particular point out right here for context, separate from causation. Anthropic says Claude Mythos Preview discovered hundreds of high-severity software program vulnerabilities and exhibits how AI can compress vulnerability discovery. That raises the bar for defenders, however the causal report in these crypto incidents factors to keys, signers, admin powers, bridge verification, RPC dependencies, and unresolved pockets publicity.
The safety implications are nonetheless severe. Quicker discovery provides attackers and defenders extra parallel floor to work by. It additionally makes outdated operational shortcuts dearer as a result of dormant secrets and techniques, privileged keys, and single-verifier paths might be examined quicker than groups can manually evaluation them.
The restore record is operational
The controls that observe from April sit above and across the codebase.
| Incident | Hidden management level | Failure mode | Sensible management |
|---|---|---|---|
| Dormant Ethereum wallets | Outdated pockets materials | Funds moved from long-idle wallets right into a tagged handle whereas the vector stays unresolved | Contemporary key technology for useful dormant funds, cautious migration, and no seed entry into unknown instruments |
| Wasabi | Admin and improve authority | Privileged function grants and UUPS upgrades enabled vault and pool drains | Key rotation, stronger thresholds, bounded admin powers, timelocks, and impartial monitoring of improve actions |
| Drift | Safety Council signer workflow | Pre-signed sturdy nonce transactions and zero-delay governance enabled quick admin takeover | Greater thresholds, delay home windows, transaction simulation, and policy-enforced co-signing |
| KelpDAO | Bridge verification path | RPC poisoning and a 1-of-1 DVN route allowed a false cross-chain message to go | Multi-DVN verification, cross-chain invariant monitoring, and impartial checks exterior the identical verifier path |


For protocols, the precedence is to cut back the quantity that any single authority can do directly. Which means time locks on admin operations, stronger and extra secure signer thresholds, monitored privileged-transaction queues, specific limits on parameter modifications, and co-signing programs that simulate transaction results earlier than people approve them.
For bridges, the precedence is impartial verification and invariant checks. A cross-chain message ought to be examined towards the financial truth it claims to characterize. If rsETH leaves one aspect, the system ought to confirm the corresponding state change on the opposite aspect earlier than the vacation spot aspect releases worth. That monitoring must exist exterior the identical path that indicators the message.
For customers, the restore record is smaller. Transfer useful outdated funds to recent keys by a course of you already belief. Separate that motion from protocol-specific approval cleanup. Deal with each declare concerning the wallet-drain root trigger as provisional till forensic work identifies a typical software, storage path, or publicity supply.
The subsequent take a look at
April proved that the common person’s safety guidelines is probably going incomplete. Audits, public contracts, and decentralized interfaces can coexist with concentrated admin authority, weak signer procedures, brittle bridge verification, and outdated pockets secrets and techniques.
The subsequent quarter will reward proof over decentralization language: constrained improve powers, seen timelocks, impartial verifier paths, transaction simulation for privileged actions, disciplined entry controls, and documented key rotation.
The dormant-wallet drains present the uncomfortable user-side model of the identical downside. A system can look quiet whereas an outdated management failure waits within the background. April’s exploit wave uncovered that layer above the code; the subsequent section will present which groups deal with it as core safety earlier than funds transfer.






