OpenAI launched a brand new cybersecurity initiative, Dawn, on Might 11, designed to search out, validate, and assist repair software program vulnerabilities earlier than attackers can exploit them.
The agency describes the strategy as making software program “resilient by design,” transferring safety earlier into the construct cycle via AI-assisted code overview, menace modeling, patch validation, and dependency evaluation.
For crypto, the place a software program failure may end up in an instantaneous capital loss inside a single block, the urgency is evident.
The usual sample within the crypto trade is reactive, going via a pre-launch audit, post-deployment monitoring, response when funds transfer, a autopsy on the tactic, vulnerability patching, reimbursement negotiation, and governance debate.
That mannequin has the weak point that the bug involves gentle solely as soon as the capital has already moved. The window between deployment and exploit is when danger runs highest, and defenses run thinnest.
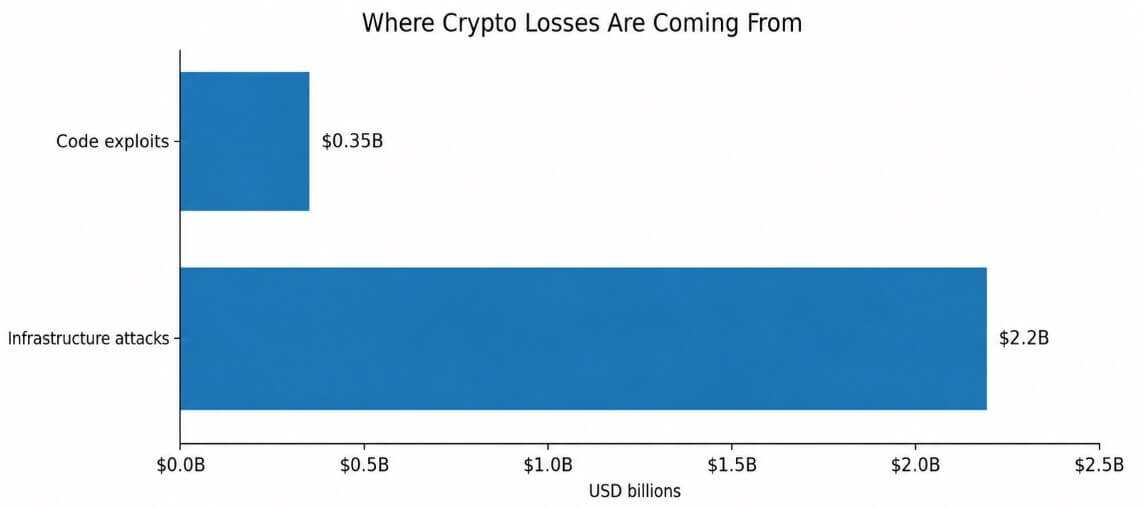
TRM Labs’ 2026 Crypto Crime Report confirmed that illicit actors stole $2.87 billion throughout practically 150 hacks and exploits in 2025. Infrastructure assaults through compromised keys, pockets infrastructure, privileged entry, front-end surfaces, and management planes drove $2.2 billion of that whole.
Code exploits, the class most audits instantly tackle, accounted for $350 million, or 12.1%.
Hacken’s knowledge for the primary quarter reinforces that audit-centric safety has actual limits, since Web3 misplaced $482 million throughout 44 incidents in a single quarter. Six of these incidents concerned audited protocols, together with one which had obtained 18 separate audits.
A $282 million theft concerned no code exploit, with the attacker bypassing the contract layer solely and compromising the operational and social infrastructure round it.
CertiK’s most up-to-date wrench-attack report famous that 34 verified bodily coercion incidents occurred globally between January and April 2026, up 41% from the identical interval in 2025, with estimated losses of roughly $101 million over these 4 months.
At that trajectory, CertiK estimates 2026 might shut with round 130 incidents. The assault vector is now the individual holding the important thing, the signer within the multisig, and the engineer with cloud console entry.
The three datasets collectively describe a menace that has migrated properly above the sensible contract.
What “resilient by design” requires in crypto
Dawn’s logic, utilized to crypto, factors towards a safety posture that runs constantly via the protocol lifecycle.
OpenAI describes AI that may purpose throughout total codebases, establish delicate vulnerabilities, validate that fixes really resolve the underlying situation, and convey that functionality into the on a regular basis build-and-deploy workflow as an ongoing perform.
For crypto, that interprets into particular operational necessities throughout the total stack the place losses are actually concentrated.
AI-assisted safe code overview operating earlier than and all through deployment would catch logic errors, access-control gaps, and unsafe assumptions earlier than they attain mainnet. Steady menace modeling throughout protocol upgrades would assess how every structure replace, oracle dependency, bridge design, or governance mechanism opens new assault surfaces.
Dependency and oracle danger evaluation would flag when a third-party integration weakens the safety mannequin of the protocol that depends on it.
Patch validation earlier than governance execution would affirm that the proposed fixes shut the vulnerability and that the fixes themselves maintain underneath adversarial circumstances.
Privileged-access overview for multisigs, signers, front-end deployments, and custody techniques would run on a daily cadence as a part of normal working procedures. Monitoring that catches irregular conduct earlier than funds depart would compress the time between detection and response.
| Safety perform | What it checks | Why it issues in crypto |
|---|---|---|
| AI-assisted safe code overview | Contract logic, entry controls, unsafe assumptions, upgrade-related bugs earlier than and through deployment | Helps catch exploitable flaws earlier than they attain mainnet, the place failure can change into instant capital loss |
| Steady menace modeling | How protocol upgrades, structure adjustments, governance mechanics, oracle hyperlinks, and bridge designs create new assault surfaces | Retains safety aligned with the protocol because it evolves, reasonably than treating danger as mounted at launch |
| Dependency and oracle danger evaluation | Whether or not third-party libraries, oracle suppliers, middleware, or bridge parts weaken the protocol’s safety mannequin | Many main failures now come from the broader stack across the contract, not the contract alone |
| Patch validation earlier than governance execution | Whether or not a proposed repair really closes the underlying vulnerability and stays protected underneath adversarial circumstances | Prevents governance from approving patches that look right however depart the exploit path open or create a brand new one |
| Privileged-access overview | Multisigs, signers, custody techniques, admin keys, cloud-console entry, and front-end deployment permissions | Infrastructure assaults more and more goal the individuals and techniques with authority to maneuver funds or change protocol conduct |
| Monitoring earlier than funds depart | Irregular transaction patterns, suspicious signer conduct, uncommon front-end adjustments, or withdrawal anomalies | Compresses the time between detection and response, giving groups an opportunity to intervene earlier than losses escalate |
Crypto protocols with in depth audit data can nonetheless have unmonitored front-end deployments or misconfigured multisigs, leaving them in an operational blind spot the place 2025’s largest losses occurred.
OpenAI stated dangerous actors can misuse expanded cyber functionality, and Dawn pairs its defensive tooling with verification, scoped entry, safeguards, misuse monitoring, and stronger account controls.
The identical AI capabilities that assist defenders overview code, validate patches, and mannequin threats will help attackers speed up phishing, generate convincing faux entrance ends, clone respectable protocols, analyze dependency chains for exploitable weaknesses, and scale social engineering throughout custodians, signers, and help channels.
Hacken’s knowledge ranked phishing among the many main assault vectors, and CertiK’s knowledge on bodily coercion confirmed attackers focusing on individuals instantly. Each classes contain social and operational manipulation, and AI operates at scale in each.
Two outcomes for crypto safety
The bull case is that “resilient by design” turns into a aggressive normal.
Protocols start treating steady code overview, signer-policy audits, dependency checks, front-end integrity monitoring, and governance-execution validation as normal necessities all through the protocol lifecycle.
In that mannequin, audit certification offers method to the total operational stack of signers, upgrades, dependencies, and entry controls proving resilience earlier than execution.
OpenAI’s personal strategy, coupling extra succesful tooling with stronger verification and course of controls, is an exterior template for that path.
In line with TRM’s knowledge, if 76% of losses come from infrastructure, that’s the place the following safety normal must function. Protocols that may show steady operational resilience would have a better time making their case with insurers, regulators, and institutional allocators than people who current solely a stack of audit certifications.
The bear case is that AI-assisted safety stays a advertising layer.
Protocols add AI-powered safety language to their documentation, and the underlying operational mannequin stays mounted in pre-launch audits and post-exploit post-mortems.
Attackers use the identical instruments to scale phishing, clone entrance ends sooner, and compromise help channels extra convincingly than defenders enhance their workflows.
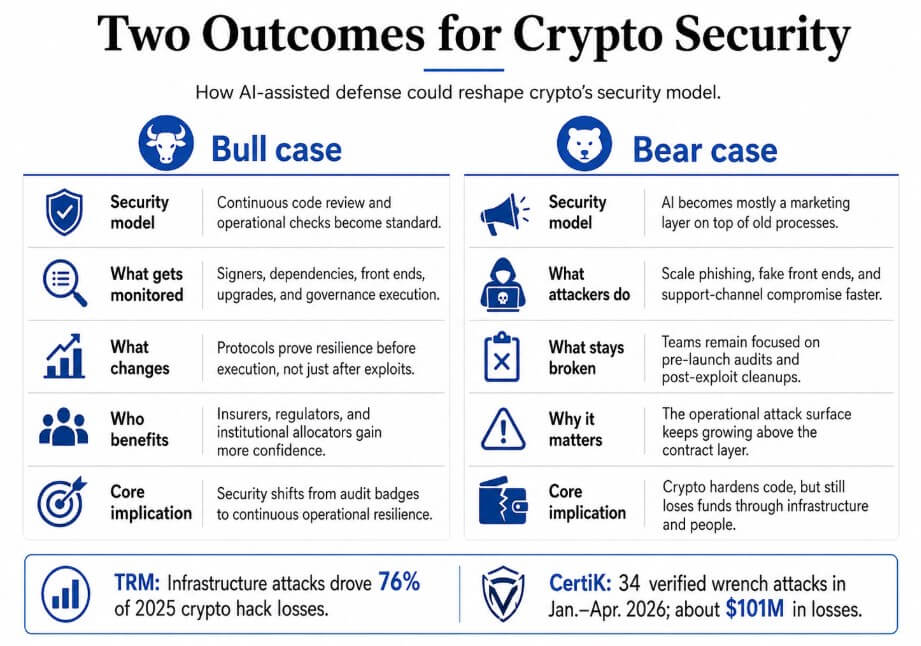
Hacken’s discovering that one attacker stole $282 million with out touching a single line of contract code reveals that the assault floor extends past the contract layer, and the trade’s present safety framework covers solely a portion of it.
The crypto trade has targeted its safety mannequin on post-exploit response and point-in-time overview, and the assault floor has moved properly past that body.
The publish OpenAI’s new cybersecurity push has a lesson for crypto: cease ready for the hack appeared first on CryptoSlate.




