The Drift exploit and Stabble’s precautionary warning level to a tough crypto safety downside: the following main breach could start lengthy earlier than funds transfer on-chain.
That’s what makes these incidents greater than remoted alarms. They recommend that some protocols should still be in search of sensible contract flaws, whereas the true publicity lies in hiring, entry, governance, and trusted relationships.
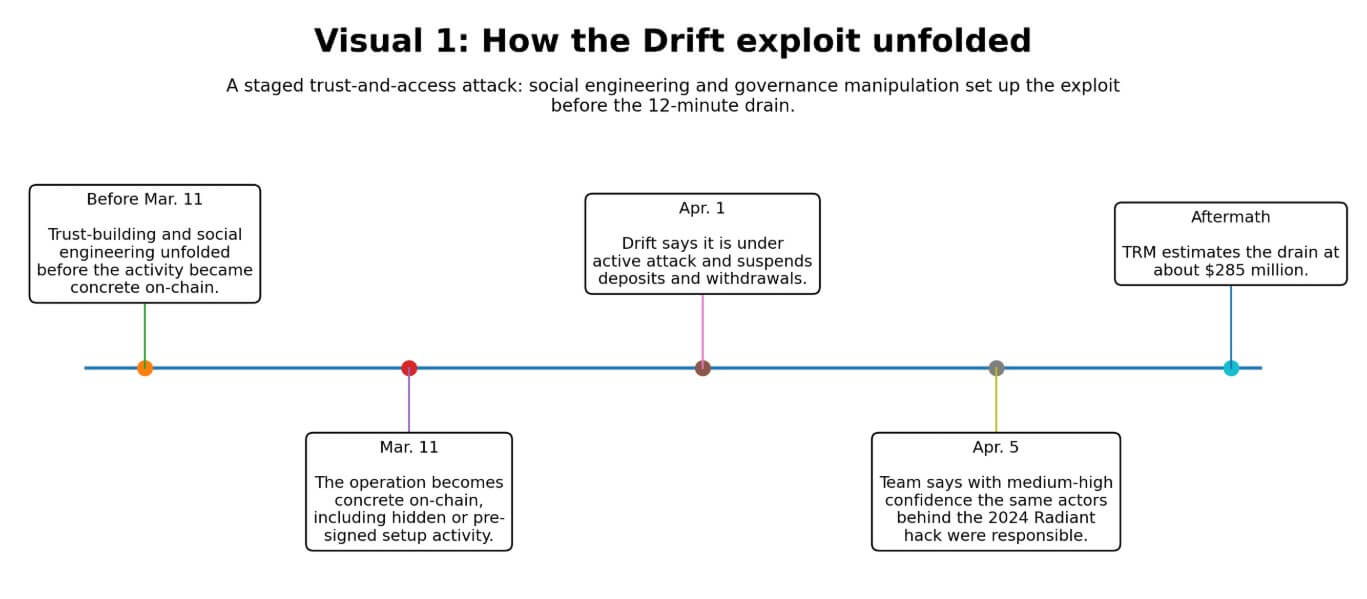
On Apr. 1, Drift suspended deposits and withdrawals and instructed customers it was underneath an lively assault.
By Apr. 5, the staff mentioned with medium-high confidence that the identical risk actors behind the October 2024 Radiant Capital hack had executed the operation.
TRM Labs estimated the drain at roughly $285 million, and the Drift autopsy described a fancy scheme wherein people used $1 million of their very own capital and met in particular person with Drift staff members to infiltrate the protocol’s construction.
On the technical aspect, TRM recognized the crucial weak point as social engineering of multisig signers mixed with a zero-timelock Safety Council migration. This governance design enabled attackers to execute privileged actions with out the delays supposed to catch unauthorized adjustments.
Elliptic mentioned the laundering patterns and community indicators matched these of prior DPRK-attributed operations and pointed to a possible compromise of administrator keys that enabled privileged withdrawals and administrative management.
Attackers earned sufficient belief to transform abnormal entry right into a 12-minute, $285 million drain.
On Apr. 7, the Solana-based liquidity protocol Stabble instructed its liquidity suppliers to withdraw funds as a precaution.
The brand new staff that just lately acquired the protocol mentioned it had found {that a} former CTO seemed to be the identical particular person ZachXBT had publicly flagged as a North Korean IT employee.
The protocol promised new audits earlier than resuming operations. What Stabble demonstrated was that alleged insider publicity now strikes customers quick sufficient to represent a reside funds occasion by itself.
The working guide already exists
Treasury’s Mar. 12 sanctions launch put numbers on the issue: DPRK IT-worker fraud schemes generated almost $800 million in 2024, utilizing fraudulent paperwork, stolen identities, and fabricated personas.
The Division of Justice individually mentioned North Korean operatives obtained employment at greater than 100 US firms utilizing faux and stolen identities. In a single Atlanta blockchain R&D case, employees stole greater than $900,000 in digital forex.
These had been workforce infiltrations sustained throughout a number of corporations over prolonged durations.
Flare and IBM X-Power revealed their operational breakdown on Mar. 18. The analysis describes a tiered construction of recruiters, facilitators, IT employees, and collaborators who help with identification verification and onboarding.
As soon as embedded, operatives use distant entry instruments, VPN and proxy providers, and inside communication channels, leaving detectable however often-missed traces in system logs.
Flare and IBM body this as a shared downside owned collectively by safety groups and HR, requiring coordination throughout hiring, onboarding, entry controls, and offboarding disciplines.
| Stage | Who’s concerned | What occurs | What the warning signal appears like | Why crypto groups miss it |
|---|---|---|---|---|
| Recruitment / identification fabrication | Recruiters, facilitators, faux candidates, collaborators | Operatives construct false personas utilizing fraudulent paperwork, stolen identities, and fabricated employment histories to get by way of screening | Inconsistent biographical particulars, skinny digital footprint, identification mismatches, suspicious references | Groups optimize for velocity and technical expertise, not adversarial hiring assessment |
| Hiring / onboarding | HR, hiring managers, collaborators / brokers, IT employees | Collaborators assist candidates cross identification verification, background checks, and onboarding steps | Uncommon assist throughout onboarding, documentation anomalies, system / location inconsistencies | Hiring and safety usually function individually, so no single staff sees the entire sample |
| Embedding inside groups | IT employees, managers, coworkers, contractors | As soon as employed, operatives set up legitimacy over time by way of routine work and trusted relationships | Heavy use of VPNs / proxies, uncommon remote-access patterns, odd system logs, restricted willingness for direct interplay | Regular remote-work conduct can masks the indications, and smaller groups lack monitoring depth |
| Entry accumulation | Builders, admins, signers, governance operators | Trusted insiders acquire permissions, signer affect, admin entry, or visibility into delicate workflows | Permission creep, over-broad function entry, weak separation of duties, dormant approvals sitting in place | Crypto safety is commonly code-centric, so human entry design will get much less scrutiny than sensible contracts |
| Exploitation / theft or extortion | Compromised insiders, exterior handlers, laundering networks | Attackers convert abnormal entry into privileged withdrawals, governance actions, key compromise, or post-access theft | Sudden use of privileged capabilities, suspicious governance migrations, uncommon withdrawal conduct, emergency pauses | By the point on-chain exercise appears irregular, the belief failure occurred a lot earlier |
| Submit-incident response | Protocol groups, customers, auditors, investigators | Groups pause operations, ask customers to withdraw, rotate entry, fee audits, and examine publicity | Precautionary withdrawal warnings, audit resets, entry evaluations, attribution updates | Most protocols do not need mature playbooks for insider-risk containment and offboarding |
Reuters reported on Mar. 31 {that a} North Korea-linked operation compromised the broadly used Axios npm package deal in a provide chain assault that might have affected thousands and thousands of environments.
The actor behind that compromise, UNC1069, is distinct from UNC4736, the cluster Drift tied to the Radiant hack. But each circumstances exploit a trusted relationship comprising a trusted particular person, a trusted signer, and a trusted package deal earlier than touching funds or techniques.
What to anticipate
The bear case runs by way of what Drift’s staging timeline exposes about latent publicity throughout DeFi.
If attackers spent from Mar. 11 to Apr. 1 embedding pre-signed authorizations and engineering approvals earlier than executing the drain, this provides to months of advanced social engineering. Different protocols could already host compromised signers, contractors, or contributors they’ve but to establish.
Stabble’s scenario, the place a suspected hyperlink to a flagged identification surfaced in ZachXBT’s public analysis earlier than the staff’s personal controls caught it, illustrates how usually organizations study their very own publicity from the skin.
Treasury’s $800 million determine for a single yr places a ground on the risk’s already value. DOJ’s 100-plus-company determine suggests the goal distribution is broad.
In that atmosphere, the following main loss could already be contained in the perimeter, ready on a governance window or an admin key rotation.
The bull case is grounded within the sector’s capability to adapt as soon as the risk mannequin turns into concrete. Drift is the concrete proof, and the countermeasures are properly documented.
Protocols can add timelocks to governance migrations, cut back signer powers, phase permissions throughout capabilities, and deal with onboarding as a safety checkpoint with the rigor utilized to code audits.
Flare and IBM provide the operational framework: confirm identification aggressively, monitor system logs and remote-access indicators, phase contractor entry, and construct offboarding self-discipline that revokes credentials and signing authority on exit. The zero-timelock governance design recognized by TRM as central to Drift’s exploit is fixable.
Protocols that repair it and add organizational controls alongside it materially slender the assault floor.
If Drift turns into a forcing occasion, because the 2016 DAO hack did, forcing a reckoning with sensible contract threat, the sector might shut the hole between recognized DPRK techniques and precise defenses inside an affordable window.
The tougher constraint on the bull case is institutional behavior. Crypto groups constructed their safety tradition round audits, bounty packages, and formal verification.
Including identification verification, entry minimization, system controls, signer separation, and HR safety coordination calls for a distinct working posture, one that almost all small-to-medium protocols have but to construct.
The market will value this in, with protocols that display governance hygiene and operational controls attracting a belief premium.
| State of affairs | What drives it | What occurs inside protocols | Market consequence | What stronger groups do otherwise |
|---|---|---|---|---|
| Bear case: latent publicity is already contained in the perimeter | Drift’s lengthy staging timeline suggests different protocols could already host compromised signers, contractors, or contributors | Groups uncover publicity late, usually after exterior analysis, suspicious exercise, or a reside incident | Extra precautionary pauses, person withdrawals, TVL fragmentation, and a belief low cost on smaller protocols | Tighten signer controls, add timelocks, rotate credentials quicker, phase permissions, and audit org entry as aggressively as code |
| Bull case: Drift turns into a forcing occasion | The sector treats Drift as a structural wake-up name, not an remoted hack | Protocols improve governance design, identification verification, onboarding checks, system monitoring, and offboarding self-discipline | Confidence regularly stabilizes, with better-defended protocols recovering belief quicker | Add timelocks to governance adjustments, decrease entry, confirm identities aggressively, and combine HR with safety operations |
| Belief-premium case: market rewards operational safety | Customers and capital start distinguishing between audited code and audited organizations | Protocols that may show governance hygiene and entry self-discipline entice stickier customers and counterparties | A premium emerges for groups with seen controls; weaker groups face increased skepticism and slower liquidity return | Publish clearer safety processes, separate signer roles, doc offboarding, monitor remote-access indicators, and present repeatable operational hygiene |
| Stagnation case: the risk is understood however habits don’t change quick sufficient | Small and mid-sized groups hold relying primarily on audits, bounties, and formal verification | Code safety improves, however hiring, entry, and trusted-software gaps stay open | Repeated “shock” incidents hold resetting confidence and elevating the price of belief | Deal with non-code controls as a part of core protocol safety, not as an elective compliance layer |
The hole above the code layer
Treasury, DOJ, Flare, IBM, TRM, and Elliptic are every, in numerous methods, pointing to the identical structural hole: sensible contract audits deal with solely the code layer.
Who holds signing keys, who vouches for contractors, who evaluations system logs, and who has the authority to push a governance migration and not using a timelock are steps that reside above that layer. The present technology of safety tooling barely reaches it.
The subsequent exploit could start with a hiring resolution, contractor onboarding, a trusted npm package deal, or a signer who, over months, earned sufficient confidence to authorize the one transaction that mattered.
Protocols that shut that hole earlier than the following attribution replace lands will nonetheless have their customers’ belief when it does.





