The rsETH disaster resulted in $200 million in dangerous debt on Aave’s books, regardless of not a single line of its contracts misbehaving.
On Apr. 18, attackers that Chainalysis preliminarily linked to Lazarus compromised RPC infrastructure, pressured a failover to poisoned nodes through DDoS, and injected false information right into a 1-of-1 DVN configuration on KelpDAO’s rsETH bridge.
The solid message launched roughly 116,500 rsETH, and Aave’s incident report confirmed that Ethereum accepted nonce 308 whereas the Unichain supply endpoint by no means superior previous 307.
The attacker equipped the compromised rsETH to Aave and borrowed towards it, leading to dangerous debt and serving as a body for the present state of DeFi’s safety.
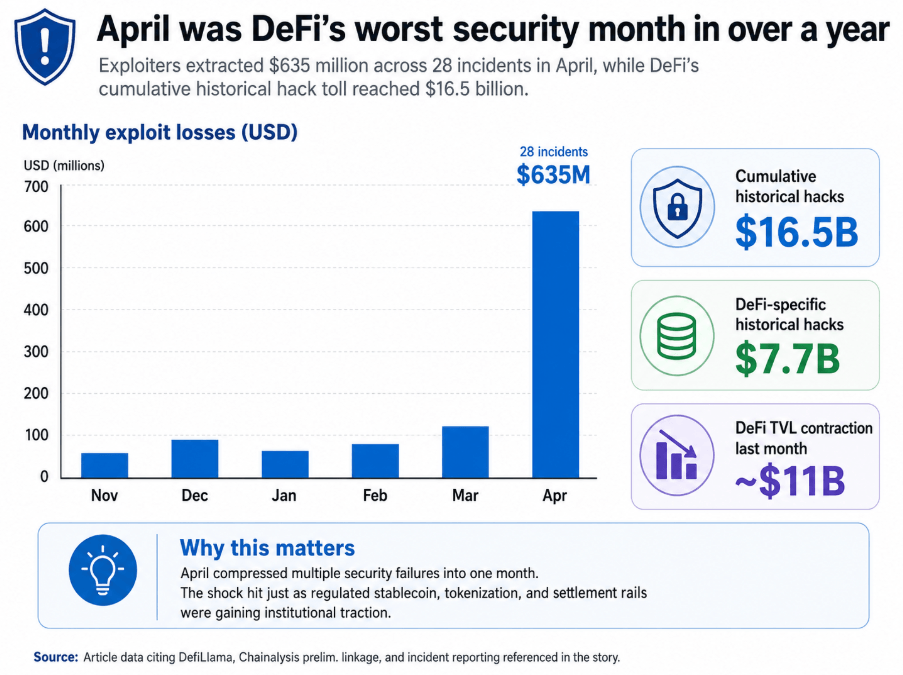
Exploiters extracted over $635 million throughout 28 incidents in April, the worst month-to-month complete in over a 12 months. DefiLlama places the cumulative historic price of hacks at $16.5 billion, with $7.7 billion particularly concentrating on DeFi.
The high-profile exploits on Drift and the KelpDAO bridge resulted in DeFi shedding almost $11 bilion in complete worth locked final month.
That contraction occurred as stablecoin rails, tokenized treasuries, and controlled settlement layers gained institutional traction in the identical capital markets.
How did DeFi find yourself right here?
Mitchell Amador, CEO of Immunefi, instructed CryptoSlate that DeFi has traditionally rewarded progress, integrations, liquidity, and velocity over safety maturity.
A protocol that provides a brand new asset, bridge, oracle, adapter, or exterior dependency positive factors speedy utility. The danger that integration carries produces no seen value sign till an exploit materializes, as a result of the absence of an incident is invisible whereas it holds.
That asymmetry stored audit cycles and isolation practices secondary to delivery velocity for years, till April concentrated the implications right into a single month.
Amador stated essentially the most neglected practices had been multisig hygiene and administration, provide chain hardening, real-time monitoring, and emergency response procedures.
Too many groups handled multisig as a safety answer in itself, when its precise energy is dependent upon signer depend, the independence of these signers, their operational setup, and the processes round transaction evaluate.
A low-threshold multisig, weak signer safety, or a poorly monitored bridge or oracle can turn into a systemic publicity as a result of DeFi protocols are composable by default. On this panorama, threat travels by way of integrations as effectively as liquidity does.
Whereas that tradition was forming inside DeFi, a special mannequin was being in-built parallel.
Solstice Finance CEO Ben Nadareski assessed:
“The hole in output per individual tells you what occurs whenever you strip away the whole lot that is not the core monetary operate. The groups that win this spherical would be the ones constructed on compliance and safety from day one, able to ship quicker than a financial institution can name a gathering about it.”
DeFi constructed composable rails for over half a decade earlier than Wall Avenue acknowledged them because the precise infrastructure layer of the subsequent monetary system.
The price of that early market place was a safety tradition calibrated for velocity over operational self-discipline.
Kasper Pawlowski, CTO of Euler Finance, names the governance dimension of the identical failure in his post-incident evaluation.
He stated:
“DeFi treats threat evaluation as a one-time onboarding choice, when in actuality threat is dynamic.”
The 1-of-1 DVN configuration that enabled the KelpDAO exploit existed in manufacturing for years. Kelp says it was the default LayerZero shipped and reviewed throughout a number of integration conferences, whereas LayerZero says Kelp downgraded to it.
Whichever account is correct, the configuration continued unflagged by way of each integration with each downstream protocol. LayerZero has since banned the configuration on a protocol-wide foundation, acknowledging that permitting its DVN to behave as the only real verifier for high-value transactions was a mistake.
| Stage | What occurred | Why it mattered |
|---|---|---|
| RPC infrastructure compromised | Attackers compromised RPC infrastructure tied to the rsETH bridge setup | The assault started exterior the core good contracts, exhibiting how off-chain infrastructure can turn into the entry level |
| DDoS pressured failover | Site visitors was pushed onto poisoned nodes by way of a pressured failover | That permit attackers management the information atmosphere seen by the bridge verifier |
| False information injected into 1-of-1 DVN | Poisoned nodes fed false information right into a single-verifier DVN configuration | A 1-of-1 verifier setup meant there was no unbiased examine to cease the solid message |
| Cast bridge message accepted | The solid message launched about 116,500 rsETH | Faux collateral was successfully minted into circulation |
| Faux rsETH equipped to Aave | The attacker deposited compromised rsETH into Aave as collateral | Aave handled the asset as legitimate and allowed borrowing towards it |
| Borrowing created dangerous debt | The attacker borrowed different belongings and left Aave with roughly $200 million in dangerous debt | Losses from a bridge failure migrated right into a lending market and had been socialized throughout the pool |
The extra consequential level is {that a} important bridge-security parameter was normalized throughout your complete dependency chain till a $292 million exploit surfaced it.
Pawlowski argued:
“The operational equipment DeFi has constructed — DAO governance, exterior threat service suppliers, and month-to-month evaluate cycles — would not transfer on the velocity the underlying threat floor does. In lots of instances, the folks doing the reviewing aren’t structurally unbiased of the belongings they’re reviewing.”
That structural battle produced the particular governance failure Pawlowski dissected. Aave’s 25,000 ETH treasury restoration proposal was authored by TokenLogic, a paid Aave service supplier that publicly lists Kelp as a consumer and operates an Aave delegate platform.
For reference, TokenLogic is similar agency voting by itself proposals. On the identical day Aave expanded rsETH to a 93% loan-to-value ratio in eMode, SparkLend deprecated the asset totally, bundling the transfer with routine cleanup of underused positions.
Three months later, that routine pruning was the one separation between Spark’s depositors and the dangerous debt Aave now carries.
One protocol’s unbiased threat judgment outperformed one other’s full-stack threat advisory equipment. DeFi’s evaluate equipment generated worse outcomes than a single asset supervisor doing portfolio hygiene.
What “right here” means
Earlier than the exploit, Aave was the most important DeFi protocol by complete worth locked, with over $26 billion in deposits.
Pawlowski famous:
“Aave was the gold customary. If Aave can carry $200 million-plus in dangerous debt from a bridge exploit on a special protocol, the market has to recalibrate what ‘protected’ really means in DeFi lending.”
The pooled lending mannequin is simply as robust as its weakest accepted collateral, and when that collateral breaks, your complete shared pool absorbs the harm. The publicity reaches each depositor within the broader market, extending nicely previous the vault that held the place.
| Protocol | Choice on rsETH | Danger posture | Consequence |
|---|---|---|---|
| Aave | Expanded rsETH to a 93% loan-to-value ratio in eMode | Extra aggressive onboarding and collateral therapy | Ended up uncovered to the compromised asset and now carries dangerous debt |
| SparkLend | Deprecated rsETH as a part of routine cleanup of underused positions | Extra conservative portfolio and itemizing hygiene | Averted the publicity that later hit Aave |
Pawlowski identified that the structural actuality had been “muted by years of ‘battle-tested’ and ‘blue-chip’ advertising and marketing.”
Amador broadened the publicity map past the mechanics of KelpDAO. The assault floor in DeFi now covers governance, signers, privileged roles, integrations, bridges, oracles, custody preparations, and each exterior system a protocol is dependent upon.
Probably the most harmful operational assumption a workforce can maintain is that audited good contracts equal a protected protocol. Immunefi’s personal analysis reveals that DeFi losses declined by as a lot as 80% over the past a number of years, as a result of the sector hardened its code and attackers tailored.
Amador added that they now examine your complete threat chain for the weakest factors, and people factors are actually off-chain, governance-adjacent, or buried in dependency stacks that no single audit covers.
For establishments, April pressured a selected reset. Amador described the guidelines now: how admin keys are managed, who can pause markets, what dependencies exist, what the incident response course of appears like, and the way shortly a menace may be contained.
Pawlowski made the identical level from the capital facet, saying establishments will proceed to enter on-chain credit score as a result of the demand for tokenized markets, clear settlement, and programmable monetary infrastructure is actual.
Nonetheless, the institutional traders will transfer towards remoted markets, permissioned or curated vaults, stricter asset onboarding, higher insurance coverage, steady monitoring, and formalized emergency controls.
Aave Horizon, a permissioned marketplace for tokenized securities and RWAs launched in August 2025, has grown to greater than $440 million in deposits.
Morpho’s vault ecosystem added ARCHITECT, the primary FINMA-licensed funding supervisor to curate vaults at scale, and Flowdesk launched an institutional AUSD vault in March 2026, utilizing tokenized equities as collateral.
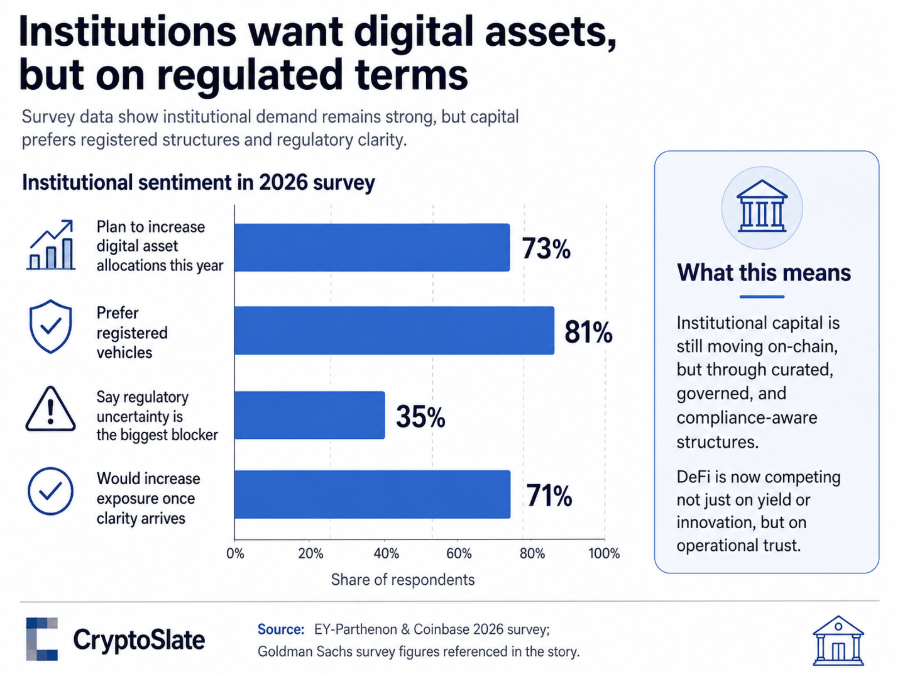
EY-Parthenon and Coinbase’s 2026 survey discovered 73% of institutional respondents plan to extend digital asset allocations this 12 months, however 81% choose registered autos. Capital is transferring on-chain by way of curated, ruled, and compliance-aware constructions.
The regulated different is accelerating on the opposite facet of that very same choice.
The GENIUS Act created the primary federal framework for US stablecoins, with obligatory 100% reserve backing, no rehypothecation, and custody requirements that Nadareski stated “learn like one thing a compliance desk may approve.”
A Goldman Sachs survey discovered 35% of institutional traders named regulatory uncertainty their largest blocker, and 71% stated they might enhance publicity as soon as readability arrived.
Nadareski stated, “The ground is in place, the capital is ready.” The CLARITY Act, which might outline jurisdictional and custodian requirements for digital belongings, together with tokenized securities, awaits consideration by the Senate Banking Committee as of Could 14.
When that passes, Nadareski argued that “the final merchandise on most institutional checklists will get checked off. The ready ends.” DeFi is competing for institutional capital towards an almost full regulatory framework.
How DeFi resurges
Pawlowski named the complete listing of DeFi restoration instruments: governance mixed with correct market isolation, automated and AI-assisted threat monitoring, selective timelocks on parameters that warrant them, circuit breakers, KYC when required by regulation, application-specific sequencing, and policy-aware block builders.
He added:
“What’s been lacking is the willingness to make use of them, as a result of each one [of the tools] entails a tradeoff towards the maximalist model of decentralization the trade has marketed itself on.”
Abandoning that advertising and marketing place is the start line, but it surely’s not straightforward.
Pawlowski famous that “the crypto trade has spent years pretending it may possibly have the whole lot”, corresponding to full decentralization, censorship resistance, institutional-grade security, and retail accessibility, with out tradeoffs.
It was “that fantasy that produced the situations for these exploits.” A regulated institutional credit score facility on-chain is a special product from a permissionless retail lending market, and governing each below the identical orthodoxy created the situations that permit aggressive rsETH listings clear governance whereas structural bridge-security parameters sat unflagged for years.
Pawlowski believes the structural repair requires ending “the conflicts that permit aggressive listings get waved by way of low-turnout governance votes by service suppliers with industrial relationships on each side of the commerce.”
SparkLend’s unbiased pruning, versus Aave’s eMode enlargement on the identical day, is proof that totally different threat philosophies yield totally different outcomes.
DeFi must institutionalize that distinction, construct governance constructions round it, and make the tradeoffs specific to each person and establishment evaluating the protocol.
Amador’s operational prescription assaults the identical drawback from the execution layer.
DeFi should professionalize safety in the identical means it professionalized liquidity incentives through steady audits, dwell bug bounty packages, formal verification the place applicable, unbiased safety councils, stronger multisig thresholds, hardware-backed key administration, real-time monitoring, public incident response playbooks, and obligatory threat evaluations for each main integration.
Circuit breakers and isolation mechanisms ought to be constructed in order that losses from a compromised asset, adapter, or dependency keep bounded throughout the affected market.
The benchmark for evaluating protocols ought to increase to cowl safety posture alongside yield and complete worth locked: who audited it, what the energetic bounty dimension is, how admin keys are managed, what dependencies exist, what the emergency process covers, and the way shortly a menace may be contained.
Customers and establishments ought to have the ability to examine protocols on these dimensions the way in which they examine APR.
| Functionality | Why it issues | What it appears like in follow |
|---|---|---|
| Market isolation | Prevents one compromised asset or dependency from contaminating a shared pool | Remoted markets, curated vaults, bounded-loss design |
| Governance independence | Reduces conflicts in asset onboarding and threat choices | Unbiased threat councils, exterior evaluate, lower-conflict voting constructions |
| Actual-time monitoring | Helps detect fast-moving failures earlier than losses unfold | Stay monitoring, AI-assisted surveillance, dependency monitoring |
| Emergency controls | Provides protocols a strategy to include incidents shortly | Circuit breakers, timelocks, pause features, emergency councils |
| Stronger key administration | Reduces admin-key and signer threat | Greater multisig thresholds, hardware-backed keys, higher signer hygiene |
| Steady safety evaluate | Retains threat evaluation dynamic quite than one-time | Necessary evaluations for main integrations, recurring audits, formal verification the place applicable |
| Incident response readiness | Improves containment and restoration when one thing breaks | Public response playbooks, restoration guardians, predefined restoration procedures |
| Safety transparency | Lets customers and establishments examine protocols past yield | Clear disclosure of audits, bounty dimension, dependencies, admin controls, and response plans |
A reform is already underway, as KelpDAO has begun migrating rsETH to Chainlink CCIP, LayerZero has banned 1-of-1 verifier configurations protocol-wide, and Aave Proposal 477 licensed liquidation of attacker positions, with recovered belongings routed to a Restoration Guardian multisig.
Part II of that proposal covers burning extra rsETH on Arbitrum, restoring bridge backing, reopening withdrawals, and compensating affected customers.
Arbitrum’s Safety Council individually froze 30,766 ETH tied to the attacker’s downstream funds.
That restoration required emergency councils, DAO votes, multisigs, and court docket proceedings, comprising a crisis-management stack drawn from the institutional finance playbook, deployed inside a system that describes itself as permissionless.
DeFi reaches for these instruments when losses get giant sufficient, and protocols can embed them prematurely or reconstruct them whereas a disaster unfolds.
DeFi’s case for composability
Nadareski recognized the particular prize at stake for establishments selecting between DeFi and controlled options.
Compliance officers need circuit breakers, time-locks, and custody requirements that match their current playbooks, and Wall Avenue has been constructing that wrapper for years.
Nadareski stated:
“The banks that transfer quickest would be the ones that cease making an attempt to construct the whole lot in-house. Spinning up on-chain settlement with legacy groups places you at 2028 if the whole lot goes proper. The play that ships this 12 months is pairing established distribution and buyer relationships with groups who have already got the rails constructed.”
Composability is DeFi’s strongest argument for holding the rails it constructed. A single protocol that executes a commerce, manages collateral, routes liquidity, and mechanically settles a transaction inside seconds represents a functionality that conventional finance can solely replicate by rebuilding from the bottom up.
Composability works as an institutional argument provided that failures keep native. As soon as a bridge verifier, a governance vote, or a compromised oracle can transmit losses throughout shared liquidity swimming pools at scale, composability operates as contagion infrastructure.
Amador famous:
“Belief the code shouldn’t be sufficient when protocols rely upon bridges, multisigs, governance processes, or exterior belongings. The brand new customary must be: assume each layer can fail, and design methods so one failure doesn’t cascade into your complete market.”
Pawlowski framed the required modifications as “rising up,” describing a sector that should settle for and publish specific tradeoffs, construct genuinely unbiased governance constructions, and make safety a product function that customers and establishments can consider and examine.
DeFi constructed the composable infrastructure that tokenized markets are actually adopting. Stablecoin rails, lending primitives, and liquidity mechanisms that originated inside permissionless DeFi are being packaged into merchandise that Wall Avenue is delivery below regulatory cowl.
If DeFi builds the operational maturity to match its technical structure, composability stays the one functionality past the attain of regulated wrappers. If DeFi fails to construct that maturity, Wall Avenue captures the stablecoin and tokenization layer and, with it, the argument that open composable finance lacked the operational self-discipline severe capital requires.



