Stablecoin issuer Circle is going through mounting scrutiny from blockchain researchers after thousands and thousands of USD Coin (USDC) had been stolen and flowed unimpeded via its proprietary bridge through the $285 million exploit of the Solana-based Drift Protocol.
The inaction through the April 1 assault, which is now the most important decentralized finance (DeFi) hack of 2026, stands in stark distinction to Circle’s aggressive asset freeze tied to a sealed US civil case simply days prior.
This juxtaposition has reignited debate over the tasks and inconsistencies of centralized stablecoin issuers working inside permissionless markets.
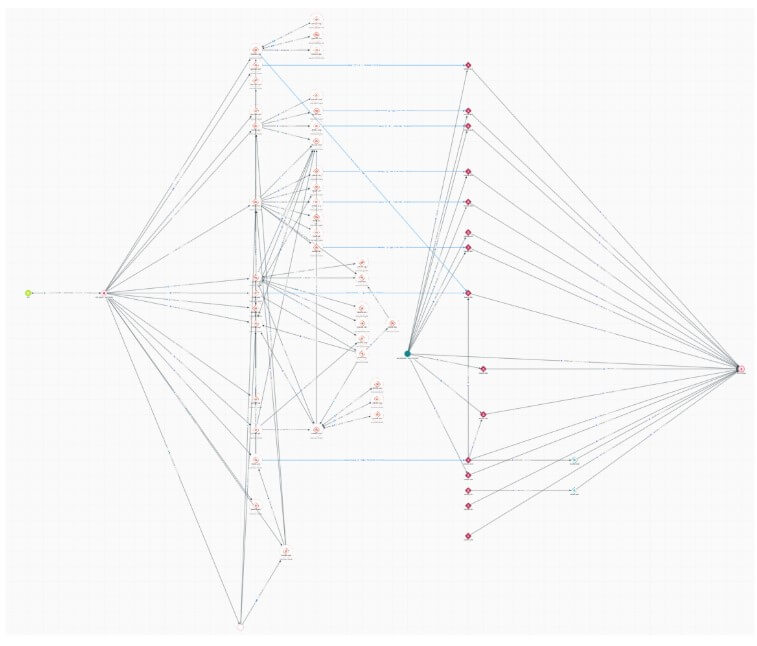
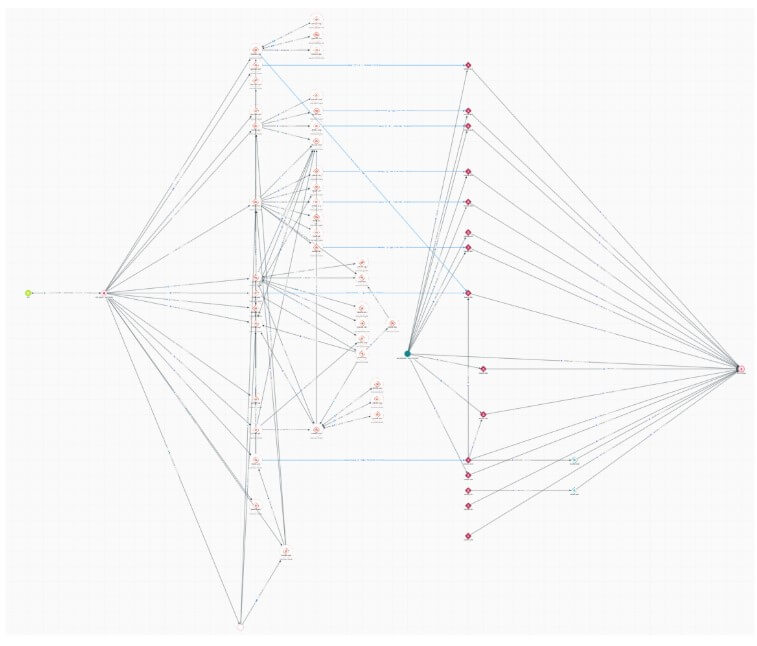
In accordance with on-chain investigator ZachXBT, the attackers bridged greater than $230 million in USDC from Solana to Ethereum throughout over 100 transactions utilizing Circle’s Cross-Chain Switch Protocol (CCTP).
Why this issues: The episode highlights a structural rigidity in crypto markets: stablecoins like USDC function inside permissionless programs however retain centralized management. When that management is utilized inconsistently, it raises new dangers for customers, protocols, and regulators making an attempt to know the place intervention will, or is not going to, happen throughout a disaster.
The transfers occurred over a number of hours through the US enterprise day, giving the New York-headquartered issuer ample time to intervene.
This view was corroborated by different safety consultants, who famous that the attacker held stolen USDC throughout a number of wallets for one to a few hours earlier than bridging to Ethereum.
The hacker notably averted changing the funds to Tether’s USDT, suggesting a calculated wager that Circle wouldn’t deploy its smart-contract blacklist authority.
That wager paid off as a result of USDT is the most important stablecoin by market capitalization, and its issuer is famend for blacklisting malicious attackers utilizing its asset to shift funds.
The civil distinction
The timing of the exploit has intensified the backlash. On March 23, Circle froze the USDC balances of 16 unrelated company scorching wallets and disrupted professional exchanges, casinos, and cost processors in response to a civil dispute.
ZachXBT beforehand characterised that motion as “probably the one most incompetent” freeze he had witnessed in 5 years.
Critics are actually asking a elementary query: If Circle claims the authority to freeze property to implement compliance, why does it apply that energy aggressively in opposition to professional companies whereas ignoring a confirmed, nine-figure heist transiting its personal infrastructure?
Nevertheless, Santisa, the pseudonymous CIO of funding agency Lucidity Cap, argued the alternative. He acknowledged:
“Circle not blacklisting is definitely fairly cypherpunk of them, irrespective of the rationale. The business pushing for energetic blacklisting places us ever additional away from decentralisation — not essentially a nasty factor! Only a trade-off.”
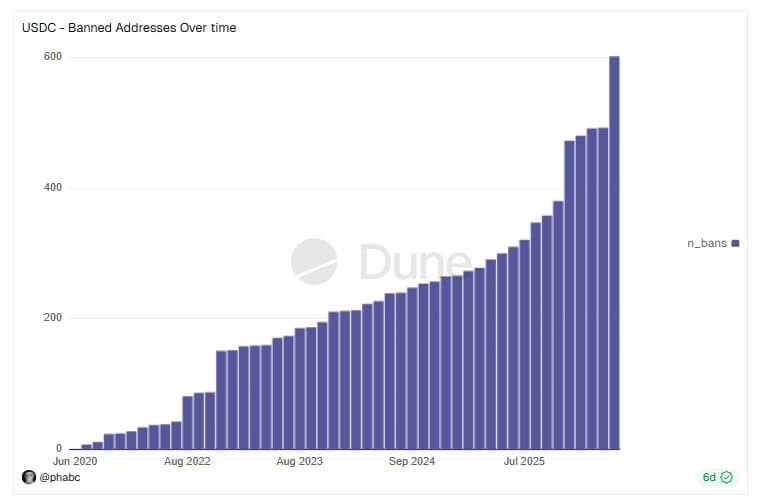
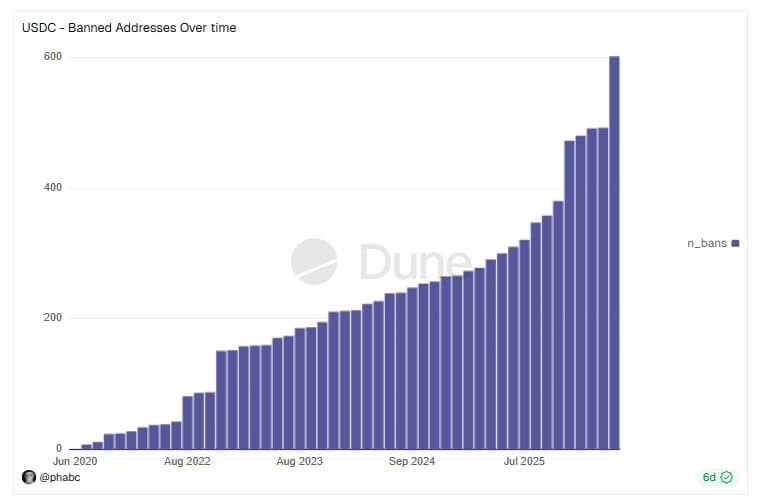
Up to now, Circle has blacklisted roughly $117 million throughout 601 wallets, based on Dune Analytics information, displaying that the aptitude exists.
Anatomy of the Drift exploit
The assault on Drift, beforehand the cornerstone of Solana’s DeFi ecosystem with over $550 million in Whole Worth Locked (TVL), was a extremely subtle, weeks-long operation.
In accordance with Drift Protocol’s autopsy, the attackers compromised the protocol’s Safety Council.
On March 30, they exploited a mechanism generally known as a “Sturdy Nonce” to quietly achieve obligatory multisig approvals.
The sturdy nonce is a device designed to maintain unconfirmed transactions legitimate indefinitely for offline approvals. Yu Xian, the founding father of blockchain safety agency Slowmist, stated:
“One other encounter with the sturdy nonce offline pre-signature mechanism exploit. This phishing approach has been prevalent for not less than 2 years. As soon as such a signature is phished away, the attacker can provoke “legally signed” on-chain operations at a future opportune second—as an example, within the Drift state of affairs, it resulted within the takeover of its on-chain admin privileges.”
On April 1, the attackers shifted admin authority, initialized a faux asset known as CVT, artificially inflated its worth by way of oracle manipulation, and borrowed in opposition to the false collateral.
In brief order, they drained the JLP Delta Impartial, SOL Tremendous Staking, and BTC Tremendous Staking vaults. DefiLlama information reveals Drift’s TVL collapsed to below $250 million following the assault.
The fallout has unfold quickly throughout the Solana DeFi ecosystem, contemplating Drift’s distinguished position.
In accordance with stories, not less than 20 third-party purposes that relied on Drift’s vaults to generate yield have confirmed monetary affect, together with Prime Numbers Fi, which estimates losses exceeding $10 million.
Who’s behind the assault?
Whereas the id of the attackers stays unknown as of press time, Drift acknowledged on X that it had recognized essential details about the events concerned within the exploit.
In the meantime, safety consultants have famous that the delicate laundering methodology factors to a well-recognized adversary of North Korean attackers.
Blockchain intelligence agency Elliptic reported that the on-chain habits and network-level indicators align with operations performed by the Democratic Folks’s Republic of Korea (DPRK).
One other blockchain safety agency, Diverg, additional acknowledged:
“We are able to affirm together with TRM Labs and Elliptic that North Korea’s Lazarus Group (TraderTraitor) [was behind the Drift attac]. [The] identical unit [was] behind Bybit’s $1.5 billion hack [and] Ronin’s $625 million assault.”
If confirmed, the Drift exploit would mark the eighteenth DPRK-linked crypto theft this 12 months, pushing the regime’s 2026 illicit haul previous $300 million.
It arrives amid an escalation in state-sponsored assaults concentrating on crypto infrastructure, together with a latest software program provide chain compromise attributed by Google to the North Korean menace actor UNC1069.






