A patch has been out there for practically a 12 months, however tens of millions of Android customers should be operating weak crypto pockets apps — leaving their funds and personal keys uncovered to a identified safety flaw.
Microsoft’s Defender Safety Analysis Staff went public final week with particulars of a vulnerability it first caught in April 2025. The flaw lived inside a broadly used software program element known as the EngageLab SDK, model 4.5.4.
As a result of that SDK is baked into hundreds of Android apps, a single malicious app might set off a series response that reached far past itself.
How The Assault Works
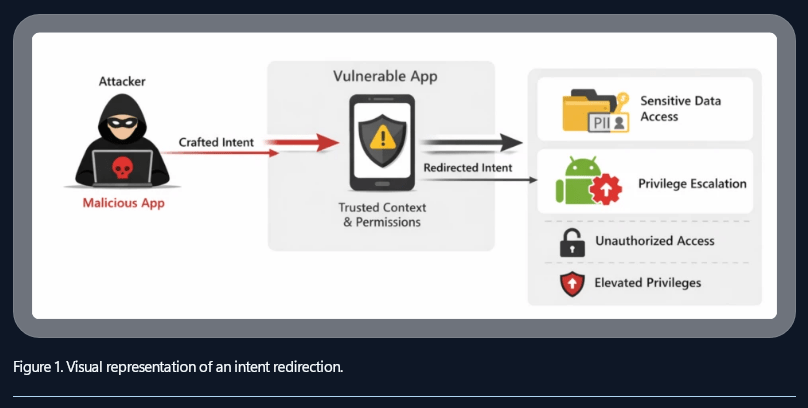
The strategy known as “intent redirection.” An attacker’s app sends a specifically crafted message to any app operating the flawed SDK model. As soon as that message lands, the focused app is tricked into handing over learn and write entry to its personal information — together with saved seed phrases and pockets addresses.
Supply: Microsoft
Android’s built-in sandbox system, which usually retains apps from seeing one another’s information, was bypassed completely. In response to Microsoft, the assault affected greater than 50 million apps throughout the Android ecosystem, with roughly 30 million of these being crypto wallets.
The vulnerability didn’t require the person to do something unsuitable. No suspicious hyperlinks. No phishing pages. Simply having the unsuitable apps put in on the identical time was sufficient.
Supply: Microsoft
Response From Microsoft And Google
Microsoft moved shortly after its discovery. By Could 2025, the corporate had introduced Google and the Android Safety Staff into the response. EngageLab launched a set model — SDK 5.2.1 — shortly after.
Experiences point out that each Microsoft and Google have since directed customers on find out how to confirm whether or not their pockets apps have been up to date by way of Google Play Defend.
BTCUSD buying and selling at $72,906 on the 24-hour chart: TradingView
Officers additionally pointed to a broader concern: apps put in as APK recordsdata from outdoors the Play Retailer are at increased threat, since they bypass the safety checks that Google applies to apps listed in its official market.
What Customers Ought to Do Now
For many customers who replace their apps often, the danger has doubtless handed. However for anybody who has not up to date since mid-2025, the really helpful motion goes past a easy app refresh.
Safety groups are advising these customers to maneuver their funds into completely new wallets, generated with recent seed phrases. Any pockets that was lively and unpatched throughout the publicity window needs to be handled as doubtlessly compromised.
The disclosure comes alongside a separate Android chip vulnerability flagged the earlier month and a brand new US Treasury initiative that pairs authorities businesses with crypto corporations to share cybersecurity risk info — an indication that cellular safety within the crypto area is drawing consideration on the highest ranges.
Featured picture from Bleeping Pc, chart from TradingView

Editorial Course of for bitcoinist is centered on delivering totally researched, correct, and unbiased content material. We uphold strict sourcing requirements, and every web page undergoes diligent evaluation by our group of prime know-how specialists and seasoned editors. This course of ensures the integrity, relevance, and worth of our content material for our readers.




